so i'll gonna to talk about SE linux
Intro?
1st. From Official Dev. of Androids
In Android 4.3, Android begins supporting Security-Enhanced Linux (SELinux), a tool for applying access control policies. SELinux enhances Android security, and contributions to it have been made by a number of companies and organizations; all Android code and contributors are publicly available for review on this same site source.android.com. With SELinux, Android can better control access to application data and system logs, reduce the effects of malicious software, and protect users from potential flaws in mobile code.
In this release, Android includes SELinux in permissive mode and a corresponding security policy that works by default across the Android Open Source Project. In permissive mode, no actions are prevented. Instead, all potential violations are logged by the kernel to dmesg. This allows Android and Android device manufacturers to gather information about errors so they may refine their software and SELinux policies before enforcing them.
2nd.From other sources
The project’s official description reads “SELinux is a security enhancement to Linux which allows users and administrators more control over access control.”
SELinux is a set of Open sourced and peer reviewed changes to the core Android Software stack to help prevent apps from performing malicious activities. This is done by establishing a set of policies that act as mandatory access controls (MAC). Depending on the policy, it can do things such as prevent apps from running or accessing specific data, to preventing root access altogether.
and what's was going on your Latest version of all android flagship phones when u meet w SELINUX
-enhance security on secure boots
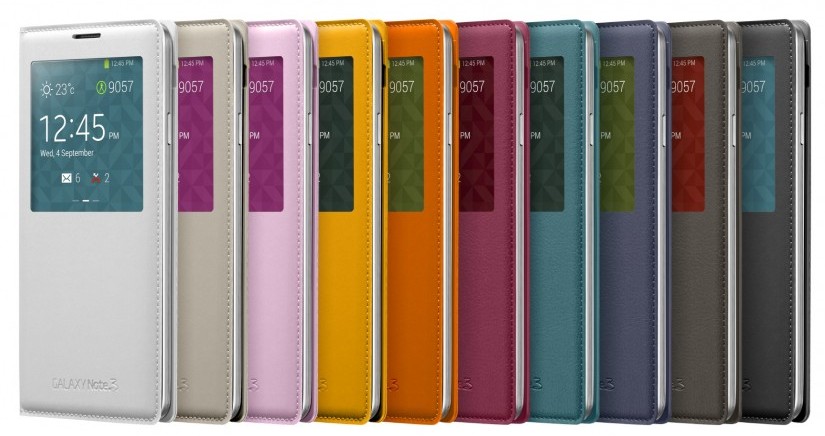
-'tight-up' your phone security such as [Samsung Knox! (similar like Find your iPhone apps)]
-once the status toasted as Enforcing, you can't do anything on flashing recovery at your phone
-kernel and rom, yes... about recovery... No...
Merge Status?
Android 4.3 is the first Android release version to fully include and enable the SELinux support contributed by the SE for Android project. The Android 4.3 SELinux support is discussed in Prior versions such as Android 4.2 included a subset of the SELinux support but not a complete, functional set, and the code was disabled by default in the build (wrapped with HAVE_SELINUX conditionals).
You can build Android 4.3 and drop in a SELinux-enabled kernel without requiring further changes if you only want the core SELinux functionality. You will still need to put the device into enforcing mode, which under Android 4.3 you can do temporarily via an adb shell su 0 setenforce 1 or permanently by putting setenforce 1 into the init.rc file (make sure the device boots and operates without denials first, as per Getting Started).
What is missing from stock Android 4.3 is:
- The new device admin APIs for managing the SELinux functionality and the SEAdmin sample device admin app for using those APIs.
- Any of the middleware MAC mechanisms, including install-time MAC, except for a restricted form of its seinfo support for labeling apps.
- The audit daemon (auditd) for collecting SELinux audit denials and writing them to /data/misc/audit/audit.log.
- Our sample policy configuration (Android 4.3 and AOSP(android open source project) master have diverged from our policy, replacing it with a policy that is fully permissive and unconfined).
- Some improvements to how policy reloading is handled, particularly avoiding the need to restart daemons.
- Proper security labeling of multi-user data directories.
If you want this additional functionality or our sample policy configuration, you will still need to download and use our modified projects as described below.
What is it?
● Mandatory Access Control (MAC) for Linux.What is it?
● Defines and enforces a system-wide security policy.
● Over all processes, objects, and operations.
● Based on security labels.
● Can confine flawed and malicious applications.
● Even ones that run as “root” / uid 0.
● Can prevent privilege escalation.
How can SELinux help Android?
● Confine privileged daemons.
● Protect them from misuse.
● Limit the damage that can be done via them.
● Sandbox and isolate apps.
● Strongly separate apps from each other and from the system.
● Prevent privilege escalation by apps.
● Provide centralized, analyzable policy.
more info, http://selinuxproject.org/~jmorris/lss2011_slides/caseforseandroid.pdf
What's the status of Selinux?
Okay, this is NOTED FOR FLASHOLICS TO READ
SELINUX can take one of these three values:
>enforcing - SELinux security policy is enforced.
>permissive - SELinux prints warnings instead of enforcing.
>disabled - No SELinux policy is loaded.
So far as my own info, you still can root your droid devices...[esp. for Samsung Galaxy S4 that already have the Samsung Knox Secure apps, try to root and flash the Previous BootLoaders and if u don't saw the Samsung Knox 'pop-out' the secure warning, u may try the Adam kernels to root and flash kernels to remove the Knox, however, your Knox flag will triggered from 0x0 to 0x1* and you can check at Odin mode aka Download mode]
Source for reading
1.https://wiki.gentoo.org/wiki/SELinux/Tutorials/How_SELinux_controls_file_and_directory_accesses
2.http://selinuxproject.org/page/SEAndroid